Networks of Care-2
Networks of care-2–
Reconstructing front-end and back-end
Neddam explores the aesthetics of software and code in profound and intricate ways. With prominent moving GIFs, a mix of different language styles (from literary poetry and invented language to audience comments), the insistence of dealing with the limitations and technical aesthetics of early computing, and the use and misuse of interactivity, mouchette.org combines elements of artistic, linguistic, computational and social cultures. mouchette.org reinforces their interdependence, pushing the aesthetic boundaries of art, while opening up societal taboos like incest, pornography and suicide. With a firm background in the arts, Neddam started as a novice on the Web. She entered a new world without a clear model of how to make art in this environment. This attitude of working without a plan, building from scratch and recycling, is very much reflected in the programming style of mouchette.org:
HTML code, in the beginning, was also something you could pick up and recycle, in a very humble, un-technical way, like Facteur Cheval picking up stones to build a palace. The knowledge came by doing. In the end the interface is totally custom made. […] I resisted CMS because of the excessive standard functions, but for the website about.mouchette.org I’m using a common CMS and it gives me a high sense of frustration, like being in a prison, having to use all kinds of predesigned boxes. […] I dream of having a software that lets me create by archiving. I am trying to find a programmer to compose an archival system within a spatial environment, an archival system that will suit Mouchette’s needs and nothing else.29
Can the attitudes reflected in the work be conserved? Over the years Neddam has continuously updated and maintained mouchette.org (Neddam 2010). The website’s success shows that her conservation strategies are effective, but is it possible to rebuild software after years have passed or an artist has died? In the past decade several successful attempts have been undertaken to restore, emulate or reconstruct software-based art. In most of these cases this was in close collaboration with the artist/programmer, but this has not led to best practices that could be used to find solutions for the conservation of these works.30 Moreover, what happens when there is no guidance from the artist/programmer? David Link’s rebuilding of LoveLettersshows that it is possible to reconstruct previously made software-based works.
LoveLetters was programmed in 1952 on a Manchester Mark I by Christopher Strachey, a fellow Cambridge student and later a working colleague of Alan Turing’s at Manchester University. The Manchester Mark I was one of the earliest electronic, programmable and universal calculating machines. The machine used Williams tubes as means of volatile storage. Strachey’s software used the Ferranti Mark I’s built-in random generator to generate over 318 billion unique love letters (Example 3.1) (Link 2006).31 Although the letters are fun,32 it is in the process of working, in other words, the context of the generator’s processes, that makes them interesting and gives additional meaning to the data.33
In 2009, David Link presented his reconstructed LoveLetters_1.0. MUC= Resurrection. A Memorial at ZKM in Karlsruhe. To build a functional replica of the Ferranti Mark I, Link worked from two archival photographs and several other documents found on the Internet, and deciphered the software from Strachey’s handwritten notes.34 As part of the travelling exhibition Fun in Software, Link’s installation was presented in 2010 at the Arnolfini in Bristol and MU in Eindhoven. The installation consisted of a Ferranti Mark I replica and some of the original working components, like the old teleprinter, the original Williams tubes, Stracey’s digitized notes and the projected love letters. Visitors could use the Ferranti Mark I by following the instructions. By toggling switches on the reconstructed interface, the user could execute Strachey’s software through its rewritten code. If someone managed to type his or her name in Baudot code on the computer’s typewriter, the resulting love letter would carry his or her signature. The new letter was then projected at the entrance to the space or somewhere on the building’s exterior. At the same time, the letter was recited through an old speakerphone placed outside the exhibition space. Stracey’s digitized notes were displayed on two vertical LCD screens near the installation. These revealed his intricate ways of thinking. The visitor was given unique insights into Link’s reconstruction process by sifting through and deciphering this information.
This is not to say that reconstructing software is an easy undertaking. Link confirms it took many years of arduous work because tracing the original equipment also turned out to be more difficult than expected. The hardware was often found by accident through university libraries or, in one instance, discovered in a dark corner of a farmer’s barn.36 Because some parts were extremely hard to find, it was necessary to emulate them. It can be argued that because the original paper notes could be accessed, reconstructing then re-executing the code was simpler. This kind of material evidence is easier to keep and read than code stored on obsolete hardware. However, as Kirschenbaum has shown, information (stored on a hard drive) leaves a trace that can be forensically reconstructed, ‘given sufficient resources – that is, elite technical and financial backing – data can be recovered from media even under the most extraordinary conditions’ (2008:xii). Those trying to re-create gaming experiences make similar statements.37 Next to reconstructing technical parts, specialized systems are devised to annotate and capture user data during the development process. This simplifies the reconstruction of the code.
As Neddam also experienced throughout the years, the reconstruction or restoration of software is possible (Neddam 2010). Nevertheless, the success of a restoration depends very much on the programmer doing it. Whereas most programmers fix problems by replacing or rewriting code into new versions – something of which Neddam is not in favour – only a few programmers take the trouble to work from the old code. For these programmers, software is not just a tool that can be adapted, emulated or used to make the work easier. For them, the fun is in the mental process of doing code that influences how they structure and think about information. As described by Niek Reus (one of Neddam’s programmers):
Before you start with the actual coding work, you visualise the results in your mind. In a sense it is close to playing chess. You try to figure out all the moves and the consequences before making the move. The actual work, the writing of code or programming, is merely typing in the final result. Sometimes a problem is technically visible, but more often there is a certain sensibility that you need to have in order to solve a specific problem.38
Even though Neddam insists on keeping the ‘original’ code, additional code is written to enable it to function properly. Although it could be argued as being variable, in most cases the ‘original’ code will change. On a practical level, an element that no longer functions because of browser settings could be made to work by adding a patch that translates the code into the new settings. This means that instead of being variable, the work is always in process, i.e., any transformation of the code gives it a different meaning.39 By translating the code, the language changes, as does the acquired meaning. Furthermore, it follows that code attains meaning in relation to specific contexts; for instance, when combined with that which lies outside of the code, or as Matthew Fuller states,
[Software] gains its power as a social or cultural artefact and process by means of a better and better accommodation to behaviours and bodies which happen on its outside.
(2008:5)
It is in light of social and contextual relations that Link’s attempt is less ‘successful’. Although he restored the functionality of the work, the historical context, meaning and function of the love letters were lost on most visitors. These could only be traced through written accounts, or in other cases, through video documentation. Furthermore, by disconnecting the various components, such as placing the typewriter on a pedestal covered by a protective glass case and shielding off the space around the Williams Tubes, a work that was once whole (defined as different elements that produce a result by working together) is now disconnected. The playful LoveLetters_1.0 still functions, but by separating and shielding some objects, it is seemingly in a state of ‘freeze’.40 As such, the material (nominal) authenticity of the machine is conserved at the expense of the conceptual (expressive) and experiential authenticity of the work. An emphasis on the physical object fits traditional conservation strategies, but shifts the focus away from setting up a system that could, for example, work with a wide variety of documents and operating systems. Such a strategy, as Ippolito also argues, would establish the rules necessary to evolve an ecosystem capable of withstanding unpredictable changes in technology. It is a future vision of self-evolving artefacts: ‘The organisms on the landscape – variations on word processors – might be interbred to produce new variations, and those judged best able to display various documents would pass their code onto the next generation of word processors’ (Rinehart and Ippolito 2014:202–3). However interesting this may be, a claim for the conceptual and the experiential over the material overlooks the importance of a media-archaeological approach that tries to open up historical paths that are themselves easily overlooked. Certainly in art, stepping away from conventional examples as well as from the endorsement of consensus is an important step.
To briefly summarize, the notion of variability is more complicated when used with software-based artworks than, say, analogue installation art. Although variability in the true sense of the word (i.e., instantiations based on the same score/code) might not be possible, digital documents contain remarkable amounts of historical information through which saved metadata can be accessed. As concluded by Kirschenbaum, ‘computer operating systems are characterized less by their supposedly ephemeral nature than by the exquisite precision of their internal environments’ (2008:204). I will return to this seemingly paradoxical situation as being both ‘variable’ and ‘processual’ in Chapter 6, where I discuss the difference between ‘fixed’ versus ‘fluid’ and ‘performative’ versus ‘processual’ processes. For the moment, it can be concluded that software is not necessarily a problem that cannot be overcome in conservation. As long as the susceptibility of specific code is comprehended, inclusive of software and the cultures around it, a website can survive for many years. However, it is important to note that the use of open standards increases the chances of survival. While it is acknowledged that using open source software in artworks benefits conservation (e.g., Kirschenbaum et al. 2009; Dekker 2010), questions around the standardization of software-based art in terms of conservation (for both open source as well as proprietary hardware and software) will likely be the greatest challenge in the (near) future.
A related issue that is often overlooked within digital data collection systems is that they often ‘assume ideal circumstances and a homogeneous data set, not the messy world of proprietary and mutually incompatible formats one gets from an individual user’s hard drive’ (Kirschenbaum et al. 2009:110). Present strategies such as cloud computing or other third-party back-up services will further complicate these matters. Another characteristic of many net artworks, and certainly of mouchette.org, is their processual nature. Websites change over time, sometimes as a result of technical changes (ranging from new browsers to screen size adjustments), or through visitor inputs. Technical variations can be traced in code, but a conservator must choose which version(s) to save (either by freezing, restoring or documenting) or with which to work (in the sense of keeping the website alive as a point of departure). Moreover, visitor input and user experience are much more difficult to trace. At the moment, this kind of information is often neglected and hard to capture. In other words, there is often only content without context.
Network of care
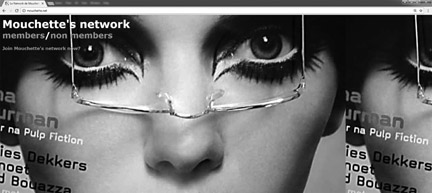
In the case of mouchette.org, users play an important part in the evolution of the work. They are invited to utilize specific elements and create their own (version of the) website. They are also interesting to consider in terms of conservation strategies. To start with the former: how can users ‘become’ Mouchette? At a certain point in the website visitors are invited to enter Mouchette’s network (Figure 3.4). They can obtain a password that enables them to act like Mouchette. With this password, texts and photographs can be uploaded to mouchette.org. E-mails sent to Mouchette may also be answered by the new inlogee. For Neddam, mouchette.org is primarily a tool for communication: a social platform that branches into several directions. First of all, mouchette.org is a playful interface, as Neddam explains, a way to express herself about issues that she as a non-native English-speaking person would find difficult to articulate (Dekker 2011a). Secondly, mouchette.org as a social platform is a space where people can communicate with or help each other. And thirdly, it allows visitors to use the website for their own projects, or to build on or re-use in their own webspaces. The latter testifies to the project’s success, as several Mouchettes have been created over the years. Moreover, the work was promoted by a close but dispersed community of followers. This could be part of the solution for its future conservation.
The term ‘network’ is used in different ways to characterize current social formations (especially within technological cultures). My intention here is not to focus on a theory of networks, but to indicate the potential of networks as collaborative practices that work towards the realization of projects. As such, the networks I’m referring to are closest to what media researchers Geert Lovink and Ned Rossiter have termed ‘orgnets’ (Lovink and Rossiter 2005; Lovink 2008:239–55). Orgnets are organized networks that should be seen in opposition to commercial social networking websites. These network formations are based on people who come together for a common purpose by building strong ties among dispersed individuals, thereby bringing goal-driven organization to the Internet. The emphasis is placed on collective intelligence (Levy 1999), or the idea of a knowledge community (Jenkins 2006), in which everyone knows something, but no one knows everything. However, I do not want to confine my use of the term ‘networks’ to technology. And following researchers Yuk Hui and Harry Halpin (2013), who lean on philosopher Gilbert Simondon’s collective individuation (1989), I want to stress collectivity in networks. Simondon’s notion of collective individuation (1989) is an interesting point of departure to analyze the underlying structures of networks. It helps to see the individual and the group not as opposing but as entities that influence each other and together constitute a constant process of individuation. As stressed by Hui and Halpin:
Psychic individuation to Simondon is more a simple individualization, which is also the condition of individuation, while collective individualisation is the process that brings the individual into a state of constant transformation […], each individual is at the same time both an agent and a milieu.
(2013:111)
A networked, community-driven conservation strategy is not unlikely to happen for mouchette.org. For instance, a situation presented itself on 23 July 2002. A few months after Neddam launched a quiz comparing characters from the film Mouchette with the website, she received a summons from Bresson’s widow to remove any reference to the film.41 Shortly afterwards, Neddam posted the letter on her website and through her e-mail lists. In response, several independent organizations took it upon themselves to mirror the project on other websites.
Similar initiatives are becoming more widespread. Instead of traditional institutions, a collection of individuals and small organizations gather to form foundations that look after an artist’s legacy. In such examples, a network of different people gathers around an initiative and starts working together. It is not uncommon for such networks to form around artworks that are not collected by museums, large institutes or private collectors: either to protect the work from censorship (as was the case with mouchette.org), or to safeguard and protect it, often after an artist dies. With different stakeholders and caretakers who do not have a centralized system or organization to manage archival information, the relationship between conservation or documentation practices and knowledge transfer becomes inherently political. In her article, ‘The Ethics and Politics of Documentation’ (2012), Van Saaze examines how collaborative knowledge production takes shape in discussions about the continued existence of an artwork, and what role documentation plays in such a process. Analyzing the documentation of Robert Smithson’s land art project Spiral Hill/Broken Circle (1971-present) shows that several stakeholders became involved in the discussions around the project’s conservation, but that reaching a solution was difficult ‘partly due to the fact that the relevant information was distributed over a wide range of archives’ (2012:81), which complicated the decision-making process. Nevertheless, the most recent restoration (in 2012) was completed as a result of individual and collective efforts by a network of caretakers. Van Saaze concludes that:
in the absence of a common heritage framework, the decision to keep this work for the future cannot be traced to one single moment in time; the history of the work shows that its prolongation had to be negotiated again and again.
(2012:82)
The distributed network of caretakers functioned through a combination of experts and non-specialists who brought in knowledge from different fields and backgrounds.42 As acknowledged by Van Saaze, a thorough investigation of the different roles and motivations of the stakeholders, or caretakers, might provide a lot of insight into the political dimensions around the artwork, as well as into the art world at the time. Moreover, analyzing the underlying structures could show how sustainable such a network can be. This shows that ‘users’ not only influence and assume ownership of the work, but that they also take care of it – at least to a certain extent. The degree to which this happens will most likely shift in time and through different networks, because the process is ever evolving, like the work itself. Nevertheless, the formation of a ‘network of care’ adds to the importance of mouchette.org.43 Besides reflecting on its own artificial conditions, it uses these conditions to set unintended, emergent and distributed events in motion. These conditions add to the work’s original ambition. Such distribution and dispersion of events is not uncommon in net art and is often what it thrives on. Similar works are, for example, Olia Lialina’s My Boyfriend Came Back From the War (1996), a unique and fascinating example of net art that keeps inspiring artists to create remakes and remixes. The outcomes are all archived in Lialina’s online Last Real Net Art Museum (1996-present).44Or, oµ4× a ‘performative action’ by Igor Štromajer who over a period of four years (from 2016 to 2020) asks a group of people to keep safe several encrypted files, which he randomly selected from his earlier project Expunction (2011) in which he deleted many of his net artworks from his server. Looking for other modes of distributing, sharing and experiencing the potential art which is stuck and compressed in those removed files, Štromajer is organising his own ‘network of care’.45 These works afford new modes of active engagement and creative use, and demonstrate a more recent way of dealing with circulation, in which the distributive effects are intentional if not foreseeable.
Although important questions remain – for example, how shifting constellations and power relations will affect future prolongation efforts of the artwork, or who will be leading or even responsible for safekeeping and tracking the documentation that is distributed across several caretakers – it is clear that these networks can operate without the structures of centralized archives and authorized custodians, which are present in most museums. For a ‘network of care’ to succeed outside of an institutional framework, or to become effective as a tool for transformation, it ideally has to consist of several characteristics. These can be traced by looking at how a network gives agency to individuals, instead of answering the question of how individuals create networks.46 A ‘network of care’ is based on a transdisciplinary attitude and a combination of professionals and non-experts who manage or work on a shared project. To enable the creation and administration of a project, the transmission of information is helped by a common mode of sharing where everyone in the group has access to all the documents or archives. Ideally, it would be an open system, or a dynamic set of tools that is used and cared for, where people could add, edit and manage information and track changes that are made. Such a system can be monitored by the network. An added bonus is that if someone leaves, the project can continue because the content and information is always accessible and part of a larger network. Such a structure allows people to take control of a shared project, thus obtaining meaning from their ‘investments’. To be able to share information and benefit from experience and insight gained elsewhere, for example, in other networks dealing with similar issues, a network should be dynamic such that individuals can easily move between networks and projects can be merged or split into separate smaller or more specialized groups.
Similarly, as mentioned, in addition to user contributions Neddam has also created several objects, performances and presentations that she considers part of mouchette.org (Dekker 2011a). When I asked her about the ‘collection’ of mouchette.org, she replied
It’s hard to say what constitutes mouchette.org. Over the years I have lost track of all the performances, projects and objects that I made. But for sure, mouchette.org is more than just a website.47
Although Neddam’s loss of memory could be questioned, it highlights that, for her, the concept of the work is the most important aspect of mouchette.org. Neddam stated:
Mouchette was about creating a form. When I started Mouchette I wanted to use the notion of a character as something that transcends media, I saw the character as something that can be used as a form, or a container, this allowed me to gather and structure information. I have always believed that a character, a person or an identity is a good metaphor. They can assume the identity of an institution without actually existing. In this sense, I see characters as containers that carry units of meaning.
(Dekker 2011a:22)
Knowledge about Neddam’s project is distributed across different (groups of) people, where each person knows something, but not everything. In other words, no single element contains the ‘whole’ story. Neddam uses relationships and situations as means to produce and distribute mouchette.org, as well as exemplify her message. This ‘social life’ of the project is important for conservators.48 It is something they will have to take into account and can benefit from. As Kathleen Fitzpatrick argues, a future conservation of digital objects may be less about:
new tools than new socially-organized systems, systems that take advantage of the number of individuals and institutions facing the same challenges and seeking the same goals. […] Context is equally important, and equally volatile, in shaping our understanding of the production, circulation, and preservation of digital texts.
(2011:126)
A dispersed network of knowledge with a non-hierarchical structure emphasizes localized knowledge, avoiding standardization and ensuring variability rather than creating a freeze state. Whereas several networks around artworks or between organizations and museums already exist, and some of them such as Inside Installations, Matters in Media Art, Variable Media Network and INCCA are, or have been, very successful, none of them have explicitly recognized or framed their work as ‘using’ the potential of ‘collective individuation’. To briefly return to Simondon (1992), in collective individuation, relations to others, to self and to technical ensembles are knotted together through processes of individuation. In other words, something becomes in relation; it ‘emerges’ from processes of becoming that are instantiated by differences. This also means that something, a technology for example, is never final or complete – it is contingent, depending on variables such as personal backgrounds, intentions, competencies or other contextual restrictions.
As for mouchette.org, I have not been able to trace every element of the website, nor will a future conservator be able to do so. However, this might not be necessary. One scenario could be that a community takes control of mouchette.org and ensures its continuation through different versions. Some parts could be physically archived or digitally stored in archives and museums; others could linger and evolve between various networks. Some of it will be automatically cached through crawlers.49 Stories could continue to be told through multiple authors and caretakers. Because Neddam does not want to control its growth, mouchette.org could keep generating more objects, events and comments. Together with communities that are growing around the website, mouchette.org is a circulation of stuff, experiences and sharing that started at some point and progresses without a fixed plan.
Collecting mouchette.org
In 2016, two decades after mouchette.org was first presented, MOTI Museum in Breda and the Stedelijk Museum Amsterdam asked Neddam if they could acquire mouchette.org. Neddam’s ideal of ‘conservation becomes creation of something new’ was put to the test. In December of that year I had several discussions with Neddam and Ward Janssen, the initiator of the acquisition and curator at MOTI. The usual questions came up: what is the work, how can it be maintained, stored, etc. However, the sheer number of projects that make up the website, and the fact that it is a 20-year-long project – and continuing, exceeded the budget by far. So Janssen suggested buying a specific project or part of the website, something that could be shown by itself and offline. Neddam did not agree. Although it was possible to sell parts of the work, as she had done in the past, this time she wanted the acquisition to be on the terms of mouchette.org. As mentioned, the website is developed in a way that all the projects interlink. However, they all connect to the database, which to Neddam forms the core of the work: the point where all the actions come together, and more importantly where the communication and information about the work is stored. It was difficult to explain that it is not merely the aesthetics, form or media, but the underlying database that needs to be conserved. Moreover, as Neddam argued, the conservation had to be done in the sense of a living database, or as ‘generative preservation’ as she came to call it: a method that acknowledges the human input (in creation and maintenance) and stresses notions of growth and expansion instead of repetition or replication.50
With the museums unable to acquire the whole work or parts of it, Neddam suggested approaching the acquisition process in different phases. For the first phase she proposed selling the museums a version of the website mouchette.org – Version 01. The concept of ‘version’ rather than ‘edition’ was important, because it signalled the time and the variability of the work, as well as its ongoing development.51 As such, Version 01 would be a ‘date-stamped’ mirror site of mouchette.org, together with documentation of the work at various times and in different ways (for instance, historical imagery and a screen capture video of the working of the site). In preparation for the second phase, supported by the museums, Neddam will investigate how the participatory aspect of the work can be transferred to others, potentially in the form of a network of care and/or by teaching someone else how to maintain the database. Also, by examining methods used by performance artists, for example, the ways Tino Sehgal transfers the knowledge about a performance to the museum; how to involve the larger community around the website – questioning and testing the value of a network of care; investigating new methods such as the blockchain and version control system for tracking changes over time – addressing the consequences of adhering to the method of versioning, while at the same time being open for other acquisitions to happen. The discussions showed the willingness of museums to follow the wishes of the artist, trying to conserve the work by allowing it to continue and change, and relinquishing the idea of a fixed version.
This chapter has shown that the resilience of net art is built and distributed through a complex and interrelated system of networks that present an assemblage of artistic, technological, political, and social relations which merge to form a variable entity. Information is produced, presented and distributed differently. Such changes impact knowledge and power relations. A focus on variability, different types of authenticities and processes opens different paths and options. Guattari (2009[1966]) proposes a paradigm in which areas that were previously not concerned with aesthetic interests have proliferated into or exploited aesthetic modes of operation. These trajectories, following Guattari, can expose and reform traditional conservation strategies by exploring various paths uncovered during the process. Consequently, a conservator should look for different strategies. Some elements of a work can be easily conserved, like posters, code, videos and music; other more ephemeral or performative elements can be documented. In conservation, multiple trails have to be followed, not single paths. Inevitably, this raises the question of whether conservators (and it could be argued conservation practices as a whole) should shift their focus from the conservation of materials to the conservation of social information and relations. And if so, would s/he still be the right person to do this? Is this still considered conservation? Does conservation need to be re-thought?
Notes